Implementing Encryption Protocols for Water Data | Implementasi Protokol Enkripsi untuk Data Air
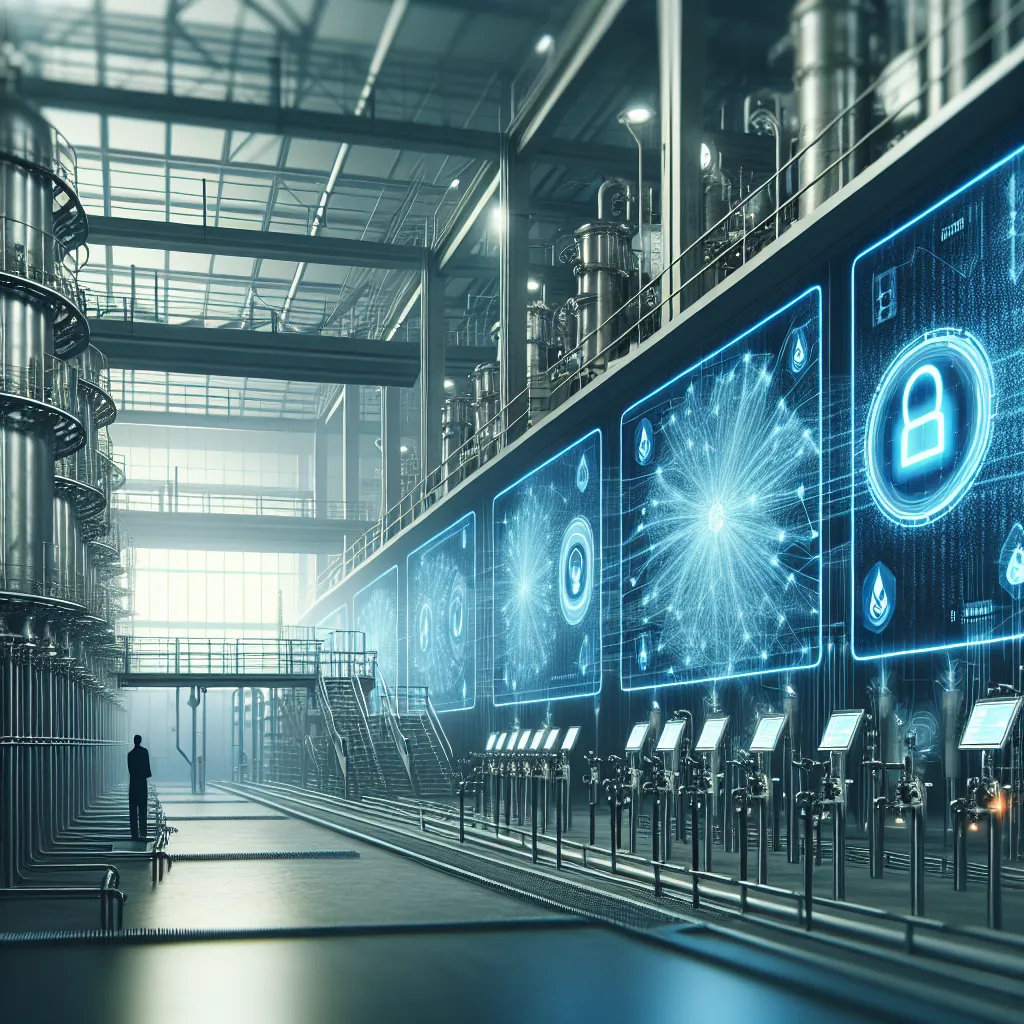
Baca dalam Bahasa Indonesia Implementing Encryption Protocols for Water Data In an age where data breaches and cyber threats loom large, safeguarding sensitive information has never been more critical. This is especially true for water utilities that handle vast amounts of data related to water supply, quality, usage, and billing. The integrity and confidentiality of this data are paramount, and implementing robust encryption protocols is an essential step toward achieving those goals.
[Read More]